The Deel/Rippling lawsuit is the first corporate espionage case where the evidence is AI-generated data trails.
Rippling filed a corporate-espionage lawsuit against Deel in March 2025, alleging that Deel had engaged in unauthorized intelligence-gathering through a Rippling employee acting as an information-source. The substantive merits of the case will work through the courts on the courts' timeline. The structurally interesting feature of the case for the operator-class observer is the evidentiary shape, which is unusual in a way that the next several years of corporate-and-employment litigation are likely to make less unusual.
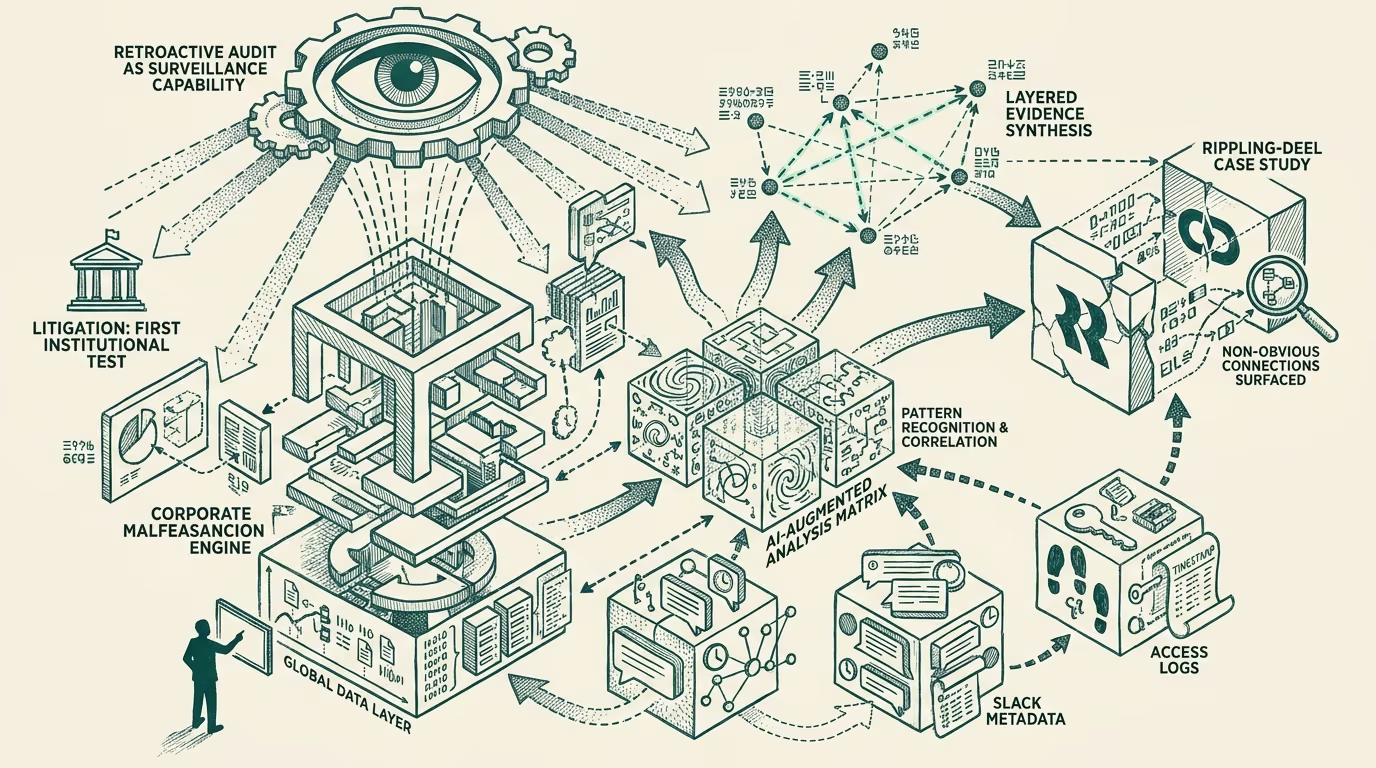
The evidence underlying the Rippling complaint is the kind of evidence that AI-augmented data-analysis infrastructure produces. The complaint draws on Slack metadata patterns (which channels the alleged-source accessed, when, with what frequency, in what cluster of activity), access-log correlations (which documents were touched, when, in what relation to other employees' access patterns), and document-classification work that surfaces non-obvious connections across the data. The patterns the complaint surfaces would have been substantially harder to identify through traditional human-review of the same data; the AI-augmented analysis produced the patterns by working across the data at scale.
The case is the first mainstream demonstration of what AI-augmented retroactive audit means for organizational security. Three implications follow.
The first is that the evidentiary bar for corporate-and-employment misconduct cases has shifted. Plaintiffs who can deploy AI-augmented analysis against the available data (the company's own logs, the publicly-available data, the discovery-class data the litigation produces) can construct evidentiary claims at substantially higher specificity than the prior decade of similar cases produced. The shift will continue through 2025-2027 as more law firms and corporate-litigation teams build the AI-augmented analysis capability.
The second is that the operational-security posture for corporate insiders has changed in ways the insiders are typically not pricing. The assumption that anomalous access patterns will be lost in the noise of routine activity is structurally less safe than it was. AI-augmented audit can identify the patterns retroactively even when the company's contemporaneous monitoring did not. The implication is that operational-security work needs to be calibrated against the retroactive-audit possibility, not just against the contemporaneous-monitoring posture.
The third is that the corporate-defendant posture in similar cases needs to engage with the evidentiary specificity the AI-augmented plaintiff can produce. Defendants whose response framework is calibrated against the prior-decade evidentiary shape will face plaintiff specificity their framework is not designed for. Defendants whose response framework engages with the AI-augmented evidentiary shape (including their own AI-augmented internal-investigation work, their own data-analysis capability, their own pattern-of-behavior reconstruction) will produce more durable defenses.
For the operator-class running organizations through 2025-2027, the practical advice is to assume that the AI-augmented retroactive audit is a feature of the litigation and regulatory environment going forward. Operational security needs to be calibrated against it. Internal-investigation infrastructure needs to be built against it. Litigation-class response infrastructure needs to engage with it.
The Deel/Rippling case is the visible inflection point. The pattern is going to continue producing similar cases at progressively-higher visibility. The operator-tier observers reading the case carefully should be calibrating the broader organizational-security and litigation-readiness posture against the new evidentiary environment. The shift is real, the implications are durable, and the operators who recognize the shift early will produce more secure organizations than the operators who do not. Build accordingly.
—TJ